Infos:
- Used Zammad version:
4.0.x - Used Zammad installation type: (source, package, docker-compose, …)
- Operating system: Ubuntu 20.04
- Browser + version:
Edge Chromium: 91.0.864.41
Firefox: 89.0
Expected behavior:
- User gets to see O365 login page
Actual behavior:
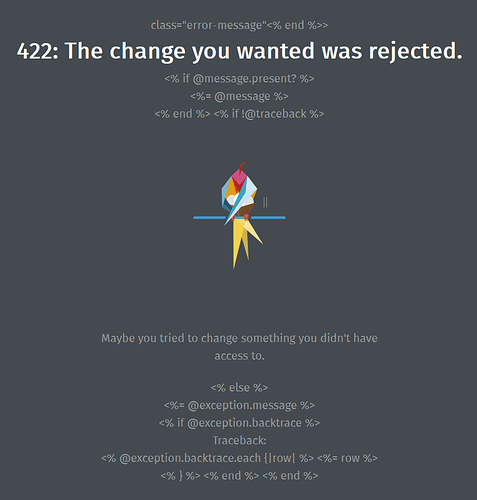
- Users see the follow message:
Steps to reproduce the behavior:
- Enable O365 login in admin. When user click on O365 login they get the message.
I followed the following guide: Microsoft / Office365 — Zammad documentation
It’s quite outdated thou, so i don’t know if i did the right thing in the new environment. I add the redirect url in my app registration in azure ad. But when i try to log in i get directed to https://zammad.domain.be/auth/microsoft_office365 with the screenshot as result. I tried changing settings in the zammad.conf like this:
proxy_set_header X-Forwarded-Ssl on;
changed proxy_set_header X-Forwarded-Proto $scheme to proxy_set_header X-Forwarded-Proto https
We use IIS reverse proxy
Our nginx config file:
this is the nginx config for zammad
upstream zammad-railsserver {
server 127.0.0.1:3000;
}
upstream zammad-websocket {
server 127.0.0.1:6042;
}
server {
listen 80;
listen [::]:80;
# replace 'localhost' with your fqdn if you want to use zammad from remote
server_name domain.be;
# security - prevent information disclosure about server version
server_tokens off;
root /opt/zammad/public;
access_log /var/log/nginx/zammad.access.log;
error_log /var/log/nginx/zammad.error.log;
client_max_body_size 50M;
location ~ ^/(assets/|robots.txt|humans.txt|favicon.ico|apple-touch-icon.png) {
expires max;
}
location /ws {
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "Upgrade";
proxy_set_header CLIENT_IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Prot https;
proxy_read_timeout 86400;
proxy_pass http://zammad-websocket;
}
location / {
proxy_set_header Host $http_host;
proxy_set_header CLIENT_IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto https;
# Change this line in an SSO setup
proxy_set_header X-Forwarded-User "";
#proxy_set_header X-Forwarded-Ssl on;
proxy_read_timeout 300;
proxy_pass http://zammad-railsserver;
gzip on;
gzip_types text/plain text/xml text/css image/svg+xml application/javascript application/x-javascript application/json application/xml;
gzip_proxied any;
}
listen [::]:443 ssl ipv6only=on; # managed by Certbot
listen 443 ssl; # managed by Certbot
ssl_certificate /etc/letsencrypt/live/domain.be/fullchain.pem; # managed by Certbot
ssl_certificate_key /etc/letsencrypt/live/domain.be/privkey.pem; # managed by Certbot
include /etc/letsencrypt/options-ssl-nginx.conf; # managed by Certbot
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; # managed by Certbot
}