Infos:
- Used Zammad version: 3.1.x
- Used Zammad installation source: (source, package, …) apt-get install
- Operating system: ubuntu
- Browser + version: any
I did find the old article from:
and confirmed that the ldap attributes have been set as described in that article
Expected behavior:
LDAP configuration should succed.
Manage → System → Integrations → LDAP → Configure
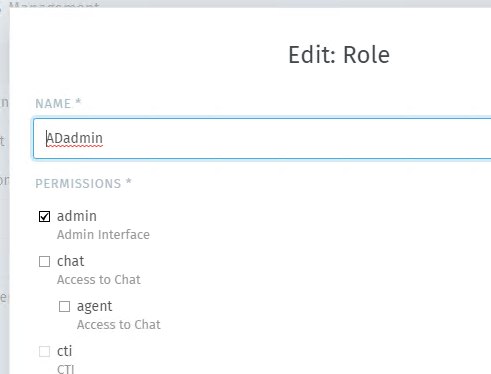
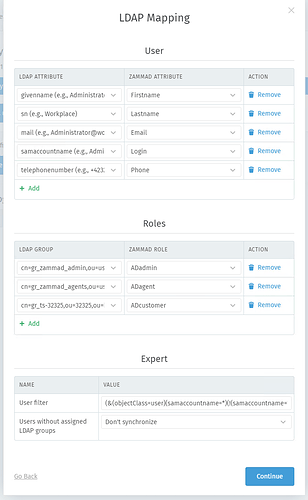
I configure everything and get as far as the LDAP Mapping configuration screen, then I add 2 Roles,
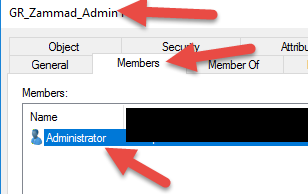
1 AD Group for Admin Role (with 1 user Administrator)
1 AD Group for Agent role ( with 3 users)
All other options are left default, also this one:
Users without assigned LDAP groups: Assign signup roles
then the mapping works and I get this message:
# LDAP Configuration
With your current configuration the following will happen:
* LDAP user to Zammad user (168):
* Users: 163 created, 1 updated, 0 untouched, 4 skipped, 0 failed, 0 deactivated
* LDAP groups to Zammad roles assignments:
* **Admin: 1** created, 0 updated, 0 untouched, 0 failed, 0 deactivated
* Agent: 3 created, 0 updated, 0 untouched, 0 failed, 0 deactivated
* Customer: 159 created, 1 updated, 0 untouched, 0 failed, 0 deactivated
…which means that the admin account gets mapped properly,
… however if I go back choose this option
Users without assigned LDAP groups: Don't synchronize
I would expect it to work as well, … it should find the admin user and not synchronize the users which are not assiged in LDAP groups, but…
Actual behavior:
as soon as I choose in the screen before (LDAP Mapping)
Users without assigned LDAP groups: Don't synchronize
and click on “Continue” then on the next screen I get this red error message:
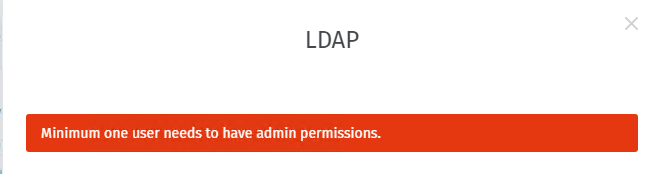
LDAP:
Minimum one user needs to have admin permissions.
Steps to reproduce the behavior:
- go as far as the LDAP Mapping window in the LDAP integration wizard
- map an AD Group “GR_zammad_admin” to the Admin Zammad Role
(above AD Group contains one user Administrator) - map a AD Group “GR_zammad_agents” to the Agent Zammand role
(above AD group contains 3 AD normal Users) - Choose the option
Users without assigned LDAP groups: Don't synchronize - Press Continue
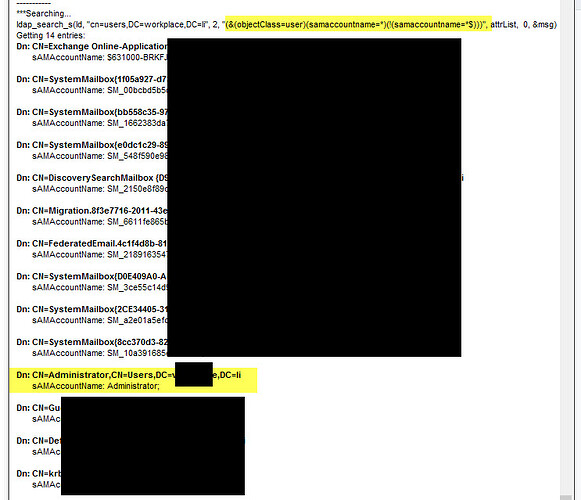
I did check that the Administrator users has all the necessary ldap attributes configured in AD on the windows side: givennamen, sn, mail, samaccountname, telephonenumber
I did not add any additional ldap attributes to the LDAP Mappings
Above attributes are configured per default in the ldap integration and I did not change them…